08.05.2025

During the Assembly Engineering Conference of Automotive Circle Assembly 2022 in Bad Nauheim (from Sept 19th – Sept 21st) there were 55 participants who contributed to the 18 presentations by very valuable comments, questions and proposals to the 26 presenters.
We presented:
“Vehicle Type Approval requires CSMS – Consequences for Automotive Production”
Focusing on the relevance of the EU regulation for CyberSecurity in Automotive Production processes, equipment and plant execution:
General Introduction - Background and idea of UNECE R155/R156 and ISO 21434/24086
General Introduction – ISO 21434 as basis for UNECE R155
Organizational Cybersecurity Management
Production related Cybersecurity Aspects
- Potential Assets (Examples)
- Vulnerabilities (Examples)

Additionally we supported by leading through the conference and fostering networking activities during breaks, exhibitions and evening activities.
Following topics were on the agenda of the conference:
• CURRENT AND FUTURE PROJECTS IN ASSEMBLYENGINEERING
• NEW CONCEPTS FOR ASSEMBLY ENGINEERING
• QUALITY MANAGEMENT AND SECURITY

The ASSEMBLY ENGINEERING INNOVATION AWARD in 2022 was given to:
Audi AG for “Modular assembly – from concept to series production”

Admin - 09:56:38
|
Add a comment
From February 18th to 19th, 2020 the Assembly Engineering Conference of Automotive Circle Assembly took place in Bad Nauheim.

The 28 presenters were proud to give insight to the 74 participants from many OEMs, Universities and Suppliers with their presentations of these topics:
• FUTURE-PROOF ASSEMBLY: FLEXIBLE AND FIT FOR NEW DRIVE TYPES
• NEW SMART FACTORY TECHNOLOGIES
• AI MEETS FINAL ASSEMBLY: HOW FINAL ASSEMBLY PROFITS FROM ARTIFICIAL INTELLIGENCE
• DIGITAL PLANNING AND ERGONOMICS
• QUALITY CONTROL AND COMMISSIONING
• IMPULSE!
We supported the 2-day-conference by taking over conference lead activities. Additionally many networking activities were triggered and maintained.

As a highlight of the conference - after its premiere at last year´s conference - the Automotive Circle confered the ASSEMBLY ENGINEERING INNOVATION AWARD again in 2020. We are very pleased at this opportunity to honor the best and most inspiring innovations applied in the series production of leading automotive manufacturers.
The winner was Volkswagen AG for:
“The transformation of Volkswagen Sachsen to electric cars – The contribution of digital planning and ergonomic work design”

Admin - 08:58:18
|
Add a comment
04.11.2019
 From September 24th to 25th, 2019 the Insight Conference of Automotive Circle Assembly took place at Magna Steyr in Graz. Overall topic was
From September 24th to 25th, 2019 the Insight Conference of Automotive Circle Assembly took place at Magna Steyr in Graz. Overall topic was
“Agile and smart: Complete vehicle manufacturing at Magna Steyr”
There were 94 participants from many European and Global OEMs and Suppliers.
The world’s largest multi OEM contract manufacturer produces a wide range of different vehicle models at one location: from the legendary Mercedes-Benz G-Class to the BMW 5 Series and Z4 to the new models Toyota GR Supra and Jaguar E-PACE and I-PACE (Car of the Year 2019).
With the production of vehicles with conventional powertrains to plug-in hybrids and the purely electrically driven I-PACE, Magna Steyr demonstrates that the company masters the agile production of different powertrains on a single line and is thus already successfully mastering a central challenge for tomorrow’s production.
As a highlight of the conference, the Magna Steyr plant in Graz has opened its doors for all participants during the morning of the second day of the conference - an experience providing exclusive insights into the assembly of the Jaguar I-PACE/E-PACE and the Mercedes G-Class production on a guided tour through the plant!
Overall topics of the presentation section were:
- Integration of electric vehicles
- Smart Factory: Nex approaches in digital planning, production and logistics
- OEM-Reports

Admin - 15:57:56
|
156 comments
20.05.2019

This year’s Gate4Spice Event was hosted by WABCO in Hannover. High-level participation of CQO and CTO revealed clearly the importance level that WABCO has internally assigned to the topic of ASPICE. To emphasize the role of different standards (ASPICE, Functional Safety and Cyber Security) and their application/relevance in truck industry, trends in commercial vehicles and the importance of Risk assessment as a proactive step was presented by Senior Director-Engineering and Project Management Quality. Amongst more presentations by Quality leadership as well as technical leadership the topic of CyberSecurity in Software development was presented by Dr. Joachim Leder providing an informal insight into concept and challenges imposed by CyberSecurity. In an interactive session around the Cybersecurity and ASPICE collaboration with Dr. Rajesh Ganji from WABCO the introduction to cyber security in automotive and also the work done by Intacs workgroup setup to reflect (Cyber)Security within ASPICE concept.
In the course of the afternoon, Joachim also led a workshop with about 20 participants out of the Gate4Spice audience. This was set up as a concept discussion – What could be provided as an input to the Cyber security workgroup by gathering proposals for improvement, changes and supporting informations.
Admin - 16:29:48
|
3365 comments
22.01.2019
 Conference subject:
Conference subject:
“Assembly in the tension field between digitalisation and IT security”
Main topics:
- Process optimization in assembly and logistics
- New technologies from the smart factory
- Cyber Security
- Human resources — the assembly worker
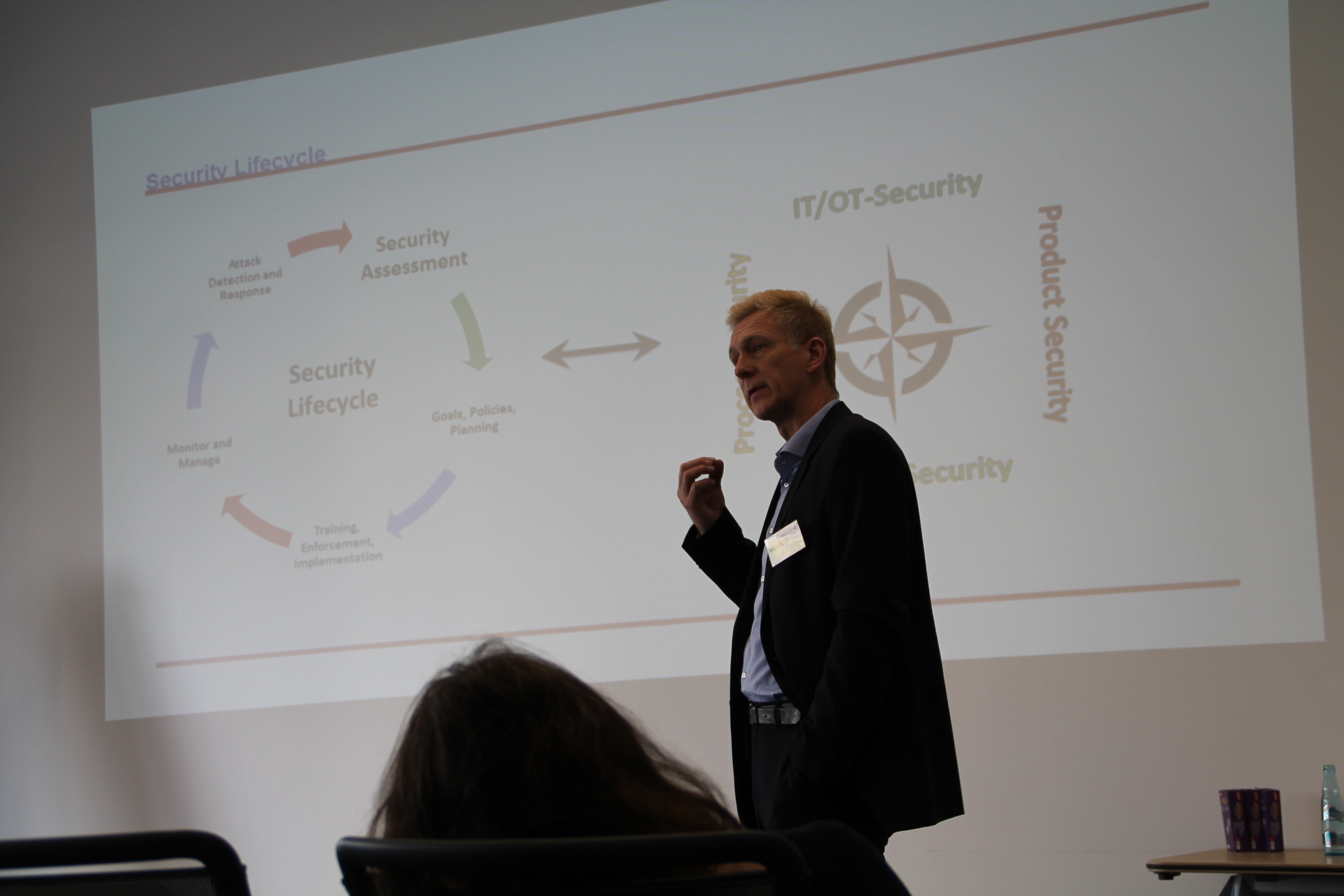
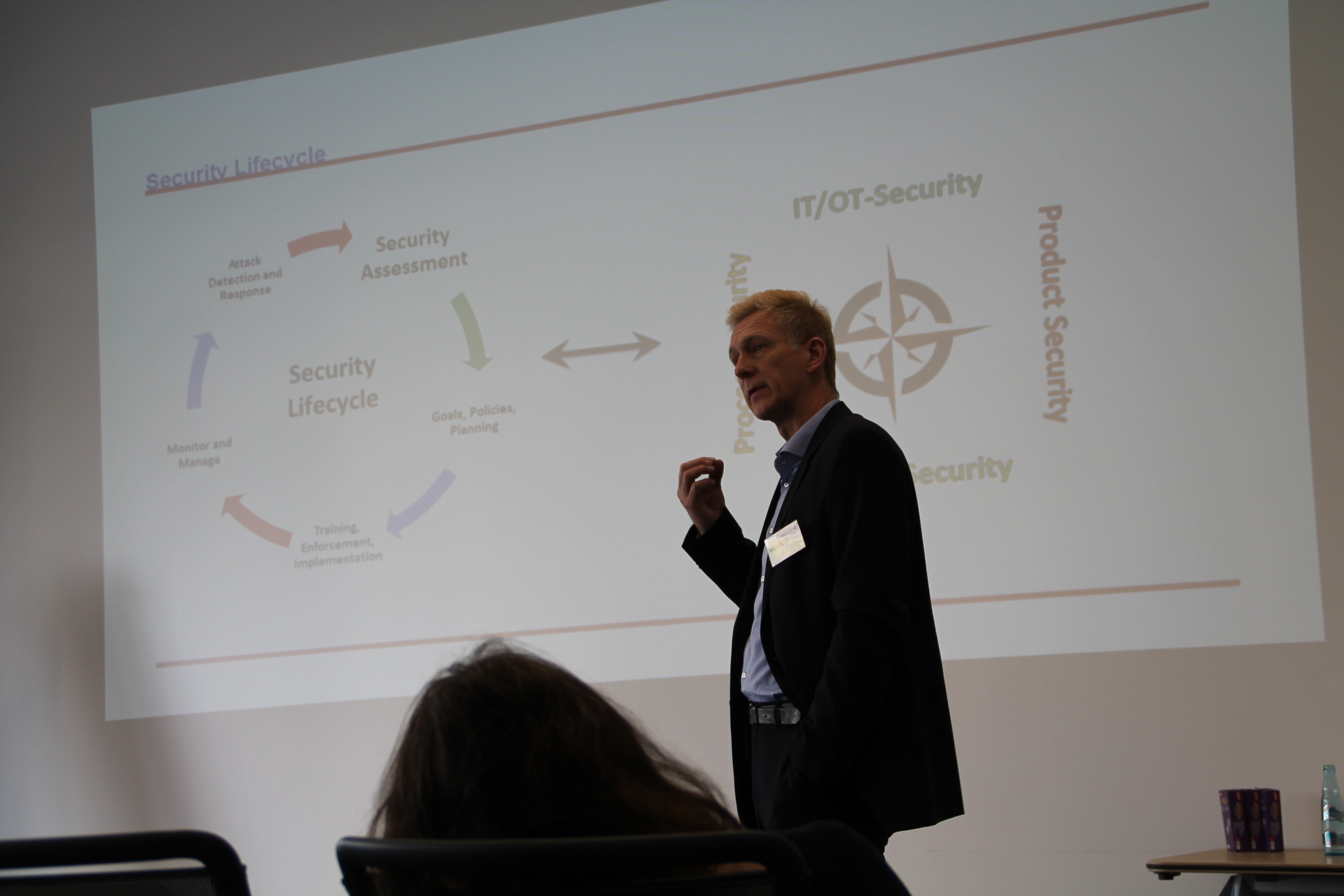
Dr. Joachim Leder presented on Wednesday, February 20th:
Risk analysis and threat analysis - the starting point of an effective security concept
Based on the concept of Security Lifecycle and the Compass Rose of Security the principles of Analysis were presented:
- System Security Analysis as the process of
> identifying the boundaries and assets of the system,
> understanding system vulnerabilities and
> evaluating possible damages
- Threat Analysis as the process of
> identifying and understanding the threats,
> their actors,
> evaluating their capabilities and motivations
- Risk Analysis as
> a combination of the results of threat and system analyses
> to create a priority-ordered list of risks and associated controls
Using the hands-on example of V2V (Vehicle - to - Vehicle) communication in an environment of autonomous driving, the process of identifying Impact Levels and combining possible attackers with respective capabilities to yield a Threat Level Matrix has been described by Joachim and an evaluation method including an algorithm patterned on ISO/SAE 21434 proposal was presented.
Finally a scenario of possible risk mitigations was included in order to demonstrate priority adaptations in the process of Planning and Execution implementation.
The presented concept and process relates directly to the given presentation of Emmanuel Ifrah from SEGULA:
OT Cyber Analytics
For the full conference agenda topics please visit: AutCircle Assembly, Bad Nauheim
Admin - 09:52:47
|
15 comments